1. Text functions - Splunk Documentation
spath(
, ) · substr( , , ) The following list contains the functions that you can use with string values.
2. How to use substr to extract the first 3 letters o... - Splunk Community
28 jan 2015 · Solved: I'm not sure I asked the right question, but I'd like to use substr to extract the first 3 letters of a field and use it as a.
I'm not sure I asked the right question, but I'd like to use substr to extract the first 3 letters of a field and use it as a grouping field. My query is as follows: * | stats sum(bytes_in) as MB by user_id as substr(user_id,1,3) | eval MB=round(MB/1024/1024,2) | sort -MB head 20 The syntax validat...
3. How to Extract substring from Splunk String using regex
14 feb 2022 · I ave a field "hostname" in splunk logs which is available in my event as "host = server.region.ab1dc2.mydomain.com".
I ave a field "hostname" in splunk logs which is available in my event as "host = server.region.ab1dc2.mydomain.com". I can refer to host with same name "host" in splunk query. I want to extract the substring with 4 digits after two dots ,for the above example , it will be "ab1d". How my splunk ...
4. Solved: How to match and filter by substr? - Splunk Community
I have a log where. labelData=123-345. or. lableData=123. How I want to ignore the -345 and just keep the first 3 characters and report on the occurances.
I have a log where labelData=123-345 or lableData=123 How I want to ignore the -345 and just keep the first 3 characters and report on the occurances. The above would count for two occurrences for labelData=123. I can't seem to figure this out using: source=*//logs/stdout.log class=myClass | fields ...
5. How to use substr in an eval with if - Splunk Community
13 dec 2021 · I try to use the query. eval ID = if(ORG="MC",ID=substr(ID,-6),0). Basically, I want in my result, if ORG="MC", I want to extract the last 6 ...
hi , Fixed the query:| eval ID=if(ORG="MC", substr(ID, -6), ID)
6. Splunk Processing Language (SPL) SubStr Function - Kinney Group
18 aug 2023 · The splunk substr function is used to manipulate strings. It is used to parse string values inside your event fields.
The splunk substr function is used to manipulate strings. It is used to parse string values inside your event fields.

7. Splunk Examples: Manipulating Text and Strings - queirozf.com
12 dec 2022 · Examples on how to perform common operations on strings within splunk queries.
Examples on how to perform common operations on strings within splunk queries.
8. Solved: how to show a substr - Splunk Community
Solved: I am doing a substr and want to see that in a table, however it just gives no results baseSearch | eval id = substr(detail.id,2,7)| table id.
I am doing a substr and want to see that in a table, however it just gives no results baseSearch | eval id = substr(detail.id,2,7)| table id I would expect to see a table of id's that have been substringed, however I get no results found?
9. How to extract substring from a string - Splunk Community
12 jul 2017 · Hi Everyone, I have a string field that contains similar values as given below: String = This is the string (generic:ggmail.com)(3245612)
Hi Everyone, I have a string field that contains similar values as given below: String = This is the string (generic:ggmail.com)(3245612) = This is the string (generic:abcdexadsfsdf.cc)(1232143) I want to extract only ggmail.com and abcdexadsfsdf.cc and remove strings before and after that. Basical...
10. String manipulation - Splunk Documentation
21 apr 2021 · Checks if a string field contains a specified substring without using regular expressions, except for the wildcard character * . Returns true if ...
Combines string values. This function accepts a variable number of arguments.
11. 2024 Splunk substring function instructions
2024 Splunk substring function instructions. herzindagi logo. Akash Yadav. 2024-07-02T23:44:26+03:00. ezutubek.info. specified length function input string ...
12. Re: Extracting key and value from substring - Splunk Community
14 nov 2023 · The syntax {_key}=mvindex(value,<
>) uses Splunk's encoding to create a new field (left hand side) that has the name of the VALUE of _key ... If you have a known max limit of keys, then you can do it without the mvexpand, which if you have a large dataset, can hit memory issues.| makeresults | eval field_id="/key1/value1/key2/value2/key3/value3/key4/value4" | rex field=field_id max_match=0 "/(?
[^/]*)/(? [^/]*)" | foreach 0 1 2 3 4 5 ...
13. Splunk Cheat Sheet: Search and Query Commands - StationX
10 mei 2024 · substr(X,Y,Z), Substring of X from start position (1-based) Y for (optional) Z characters, substr("string", 1, 3) #str. time(), Current time to ...
Use this comprehensive splunk cheat sheet to easily lookup any command you need. It includes a special search and copy function.

14. Solved: How to get a substr from a fields name - Splunk Community
Now coming to actual question. Since you have Six fixed columns and based on specific column clicked each column needs to be broken in separate columns. You can ...
Hi everyone, I want to deliver 2 fields with 1 parameter to a destination panel. I deliver the string JNL_, the first number contains the first field and the second number contains the second field . For example "JNL000_01E" (it's in HEXA), the first field name is "JNL000" and the second is "JNL01E"...
15. How get a total count based on the substring value... - Splunk Community
13 jun 2023 · Solved: Below is the splunk query, (My.Message has many various types of messages but the below one is what I wanted) index="myIndex"
Below is the splunk query, (My.Message has many various types of messages but the below one is what I wanted) index="myIndex" app_name="myappName" My.Message = "*symbolName:*" When I run the above query, I get the below results: myappstatus got Created, symbolName: AAPL ElapsedTime: 0.0002009 m...

16. Log queries | Grafana Loki documentation
splunk logo Splunk. datadog logo Datadog. new relic logo New Relic. snowflake ... Keep log lines that contain a substring that starts with error= , and is ...
Overview of how log queries are constructed and parsed.

17. 2024 Splunk substring function not
3 dagen geleden · ... substr function working version whereas version splunk seems supporting checked. HerZindagi. start index length substring. field given. looks ...
18. How do I get a substring from a field after the "_" character?
20 feb 2019 · ... substring to a. ... Splunk, Splunk>, Turn Data Into Doing, Data-to-Everything, and D2E ...
I have a string as ABCD_20190219_XYZ I need to get 20190219 like 8 characters after first "_" and than convert that substring to a date. Thanks
19. Migrate Splunk detection rules to Microsoft Sentinel
11 mrt 2024 · Learn how to identify, compare, and migrate your Splunk detection rules to Microsoft Sentinel built-in rules ... substr("string", 1, 3), substring ...
Learn how to identify, compare, and migrate your Splunk detection rules to Microsoft Sentinel built-in rules.

20. Eval Functions - LCN Services
substr(X,Y,Z), Returns a substring field X from start position (1-based) Y ... Returns the URL X decoded. urldecode("http%3A%2F%2Fwww.splunk.com%2Fdownload%3Fr% ...
The eval command calculates an expression and puts the resulting value into a field (e.g. “…| eval force = mass * acceleration”). The following table lists the functions eval understands, in addition to basic arithmetic operators (+ – * / %), string concatenation (e.g., ‘…| eval name = last . “, ” . last’), boolean operations (AND OR NOT XOR < > <= >= != = == LIKE)
21. Splunk integration - Moogsoft
23 feb 2024 · Extract Substring action · Filter action · Format Timestamp action · Match ... Use the commands addmoogsoftevent and removemoogsoftevent , in ...
This integration ingests Splunk alerts and maps them to APEX AIOps Incident Management events automatically.
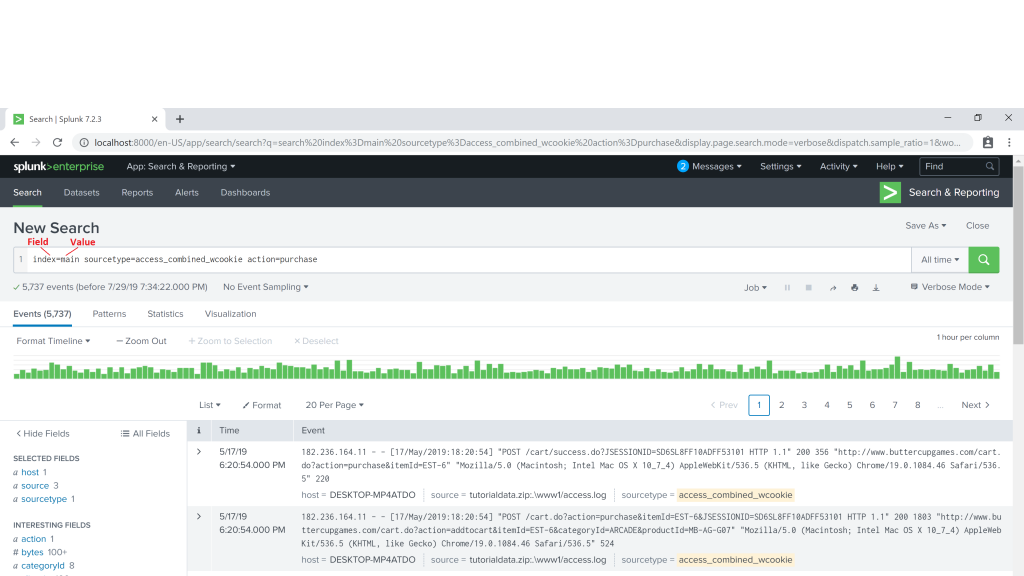
22. A Beginner's Guide to Regular Expressions in Splunk - Kinney Group
19 apr 2024 · This beginner's guide to Splunk regex explains how to search text to find pattern matches in your data. Regex is a data filtering tool.
This beginner's guide to Splunk regex explains how to search text to find pattern matches in your data. Regex is a data filtering tool.
23. Transform data | Grafana documentation
splunk logo Splunk. datadog logo Datadog. new relic logo New Relic. snowflake logo Snowflake · All monitoring and visualization solutions. Stay up to date.
Use transformations to rename fields, join time series/SQL-like data, apply mathematical operations, and more

24. Eval Substring Match? - Splunk Community
17 sep 2021 · Anyone have a good method for doing substring matches where field1 is my searched field and field2 is my substring I want to search for?
Anyone have a good method for doing substring matches where field1 is my searched field and field2 is my substring I want to search for? Attempted to use the following logic without any luck and running low on ideas. | eval comparison = if(like(field1, %field2%), "1", "0") field1 is a URL and fie...
25. How to use rex command to extract fields in Splunk?
12 aug 2019 · One of the most powerful features of Splunk, the market leader in log aggregation and operational data intelligence, is the ability to ...
Tweet One of the most powerful features of Splunk, the market leader in log aggregation and operational data intelligence, is the ability to extract fields while searching for data. Unfortunately, it can be a daunting task to get this working correctly. In this article, I’ll explain how you can extract fields using Splunk SPL’s rex command. […]